[sc name=”ad_1″] If the connectivity and security of your organization rely on Cisco RV320 or RV325 Dual Gigabit WAN VPN routers, then you need to...
[sc name=”ad_1″] Security researchers have discovered two separate malware campaigns, one of which is distributing the Ursnif data-stealing trojan and the...
[sc name=”ad_1″] China has blocked Microsoft-owned search engine Bing, the company confirmed after receiving complaints from users throughout the country who...
[sc name=”ad_1″] It is 2019, and millions of computers still either have at least one outdated application installed or run outdated operating systems...
[sc name=”ad_1″] The U.S. Department of Homeland Security (DHS) has today issued an “emergency directive” to all federal agencies ordering IT...
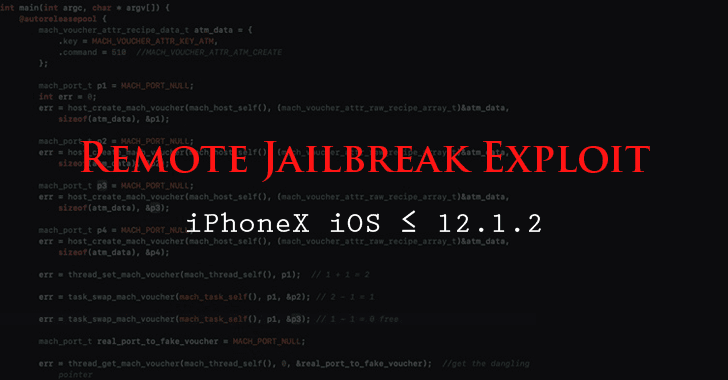
[sc name=”ad_1″] Here we have great news for all iPhone Jailbreak lovers and concerning one for the rest of iPhone users. A Chinese cybersecurity researcher...
[sc name=”ad_1″] Beware! If you have downloaded PHP PEAR package manager from its official website in past 6 months, we are sorry to say that your server...
[sc name=”ad_1″] Just in time… Cybersecurity experts this week fighting over Twitter in favor of not using HTTPS and suggesting software developers to only...
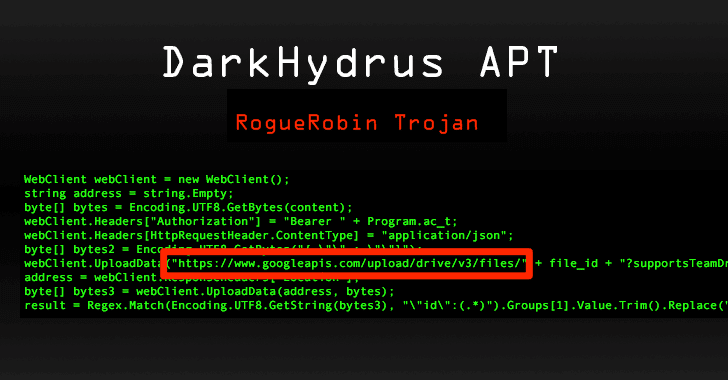
[sc name=”ad_1″] Since most security tools also keep an eye on the network traffic to detect malicious IP addresses, attackers are increasingly adopting...
[sc name=”ad_1″] The French data protection watchdog CNIL has issued its first fine of €50 million (around $57 million) under the European Union’s new...