[sc name=”ad_1″] Justniffer is a network protocol analyzer that captures network traffic and produces logs in a customized way, can emulate Apache web server...
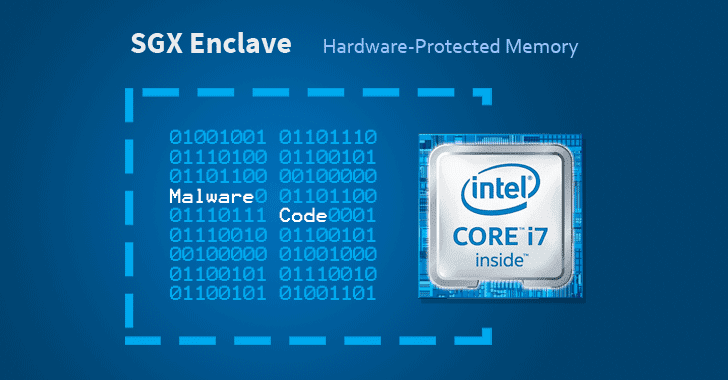
[sc name=”ad_1″] Cybersecurity researchers have discovered a way to hide malicious code in Intel SGX enclaves, a hardware-based memory encryption feature in...
[sc name=”ad_1″] Ubuntu and some other Linux distributions suffer from a severe privilege escalation vulnerability that could allow a local attacker or a...
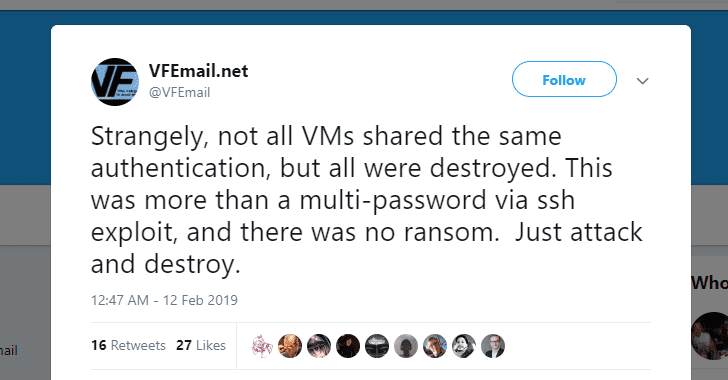
[sc name=”ad_1″] What could be more frightening than a service informing you that all your data is gone—every file and every backup servers are entirely...
[sc name=”ad_1″] Welcome back! Adobe has today released its monthly security updates to address a total of 75 security vulnerabilities across its various...
[sc name=”ad_1″] A new security vulnerability has been discovered in the latest version of Apple’s macOS Mojave that could allow a malicious...
[sc name=”ad_1″] Microsoft has issued its second Patch Tuesday for this year to address a total of 77 CVE-listed security vulnerabilities in its Windows...
[sc name=”ad_1″] Smart devices definitely make our lives easier, faster, and more efficient, but unfortunately, an insecure smart device can also ruin your...
[sc name=”ad_1″] A malicious Windows EXE file can even infect your Mac computer as well. Yes, you heard me right — a .exe malware on macOS. Security...
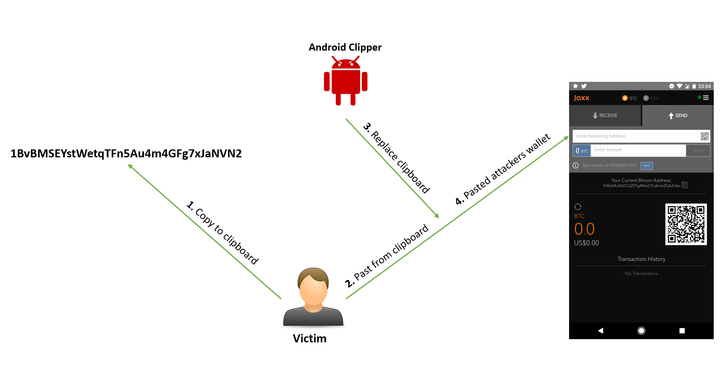
[sc name=”ad_1″] A security researcher has discovered yet another cryptocurrency-stealing malware on the official Google Play Store that was designed to...