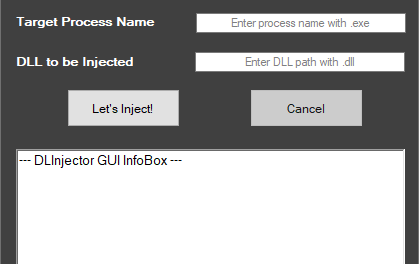
[sc name=”ad_1″] DLInjector for Graphical User Interface. Faster DLL Injector for processes. It targets the process name to identify the target. The process...
[sc name=”ad_1″] xeca is a project that creates encrypted PowerShell payloads for offensive purposes. Creating position independent shellcode from DLL files...
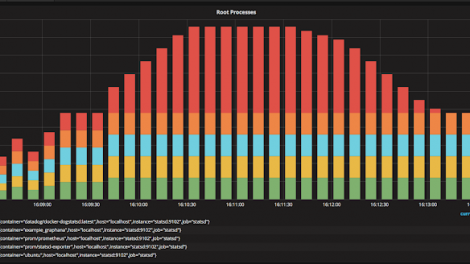
[sc name=”ad_1″] cnitch (snitch or container snitch) is a simple framework and command line tool for monitoring Docker containers to identify any processes...
[sc name=”ad_1″] Mística is a tool that allows to embed data into application layer protocol fields, with the goal of establishing a bi-directional channel...
[sc name=”ad_1″] DeimosC2 is a post-exploitation Command & Control (C2) tool that leverages multiple communication methods in order to control machines...
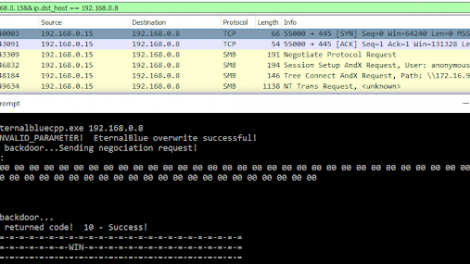
[sc name=”ad_1″] EternalBlue suite remade in C which includes: MS17-010 Exploit, EternalBlue/MS17-010 vulnerability detector, DoublePulsar detector and...
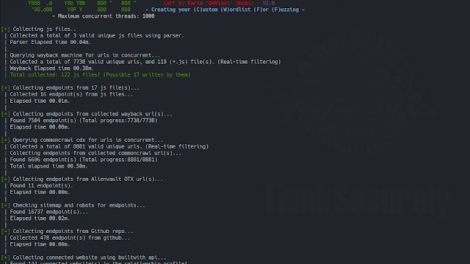
[sc name=”ad_1″] CWFF is a tool that creates a special High quality fuzzing/content discovery wordlist for you at the highest speed possible using...
[sc name=”ad_1″] Cloudsplaining is an AWS IAM Security Assessment tool that identifies violations of least privilege and generates a risk-prioritized HTML...
[sc name=”ad_1″] A tool that detects the privilege escalation vulnerabilities caused by misconfigurations and missing updates in the Windows operating...
[sc name=”ad_1″] Kubei is a vulnerabilities scanning tool that allows users to get an accurate and immediate risk assessment of their kubernetes clusters...