Python script that gets Twitter users’ tweets location
Features
- Gets Twitter Usernames based on a latitude and longitude
- Profiles URLs
- Tweet Latitude and Longitude
- Google Maps link to Latitude and Longitude
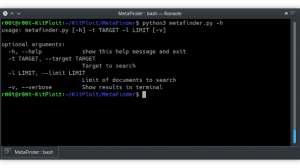
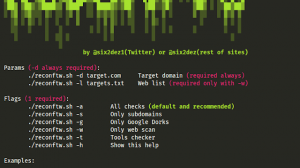
Usage
TwLocation should work on all Linux distros running Python 2.7 First, clone it by entering the following command in the terminal
git clone https://github.com/MazenElzanaty/TwLocation.git
Now naviagte to TwLocation directory
cd TwLocation
Now install the requirements with the following command
pip install -r requirements.txt
Edit config.txt and put your twitter app keys
cat config.txt
consumer_key = "XxXxXxxXXXxxxxXXXxXX"
consumer_secret = "xXXXXXXXXxxxxXxXXxxXxxXXxXxXxxxxXxXXxxxXXx"
access_key = "XXXXXXXX-xxXXxXXxxXxxxXxXXxXxXxXxxxXxxxxXxXXxXxxXX"
access_secret = "XxXXXXXXXXxxxXXXxXXxXxXxxXXXXXxXxxXXXXx"
Now you can run TwLocation
python TwLocation.py
Video
https://youtu.be/VuCOE8PwJDs



















Add Comment