WhatWaf is an advanced firewall detection tool who’s goal is to give you the idea of “There’s a WAF?”. WhatWaf works by detecting a firewall on a web application, and attempting to detect a bypass (or two) for said firewall, on the specified target.
Features
- Ability to run on a single URL with the
-u/--urlflag - Ability to run through a list of URL’s with the
-l/--listflag - Ability to detect over 40 different firewalls
- Ability to try over 20 different tampering techniques
- Ability to pass your own payloads either from a file or from the terminal
- Payloads that are guaranteed to produce at least one WAF triggering
- Ability to bypass firewalls using both SQLi techniques and cross site scripting techniques
- Ability to run behind Tor
- Ability to run behind multiple proxy types (
socks4,socks5,http,https) - Ability to use a random user agent, personal user agent, or custom default user agent
- More to come…
Installation
Installing whatwaf is super easy, all you have to do is the following:
Have Python 2.7, Python 3.x compatibility is being implemented soon:
sudo -s << EOF
git clone https://github.com/ekultek/whatwaf.git
cd whatwaf
chmod +x whatwaf.py
pip2 install -r requirements.txt
./whatwaf.py --helpProof of concept
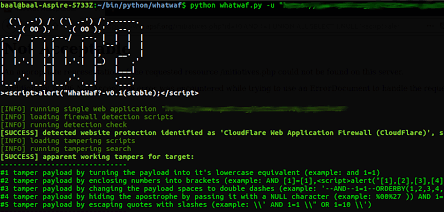
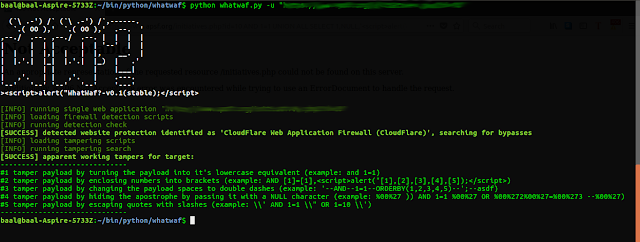
First we’ll run the website through WhatWaf and figure out which firewall protects it (if any):
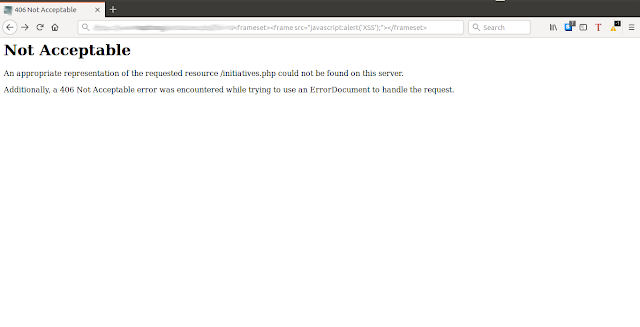
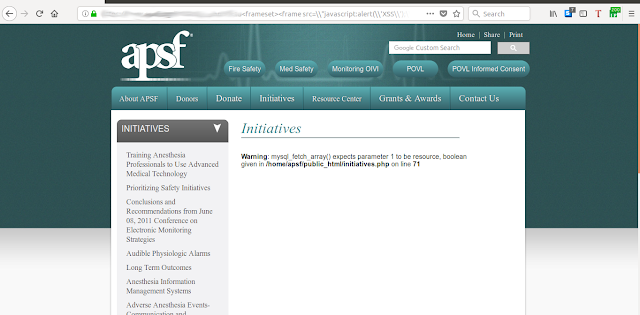
Next we’ll go to that website and see what the page looks like:
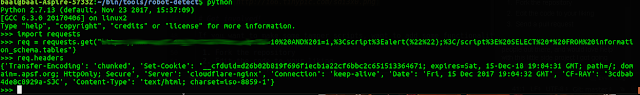
Hmm.. that doesn’t really look like Cloudflare does it? Let’s check what the HTTP headers server and cookies say:
And finally, lets try one of the bypasses that it tells us to try:



















Add Comment