[sc name=”ad_1″]
Saferwall is an open source malware analysis platform.
It aims for the following goals:
- Provide a collaborative platform to share samples among malware researchers.
- Acts as a system expert, to help researchers generates an automated malware analysis report.
- Hunting platform to find new malwares.
- Quality ensurance for signature before releasing.
Features
- Static analysis:
- Crypto hashes, packer identification
- Strings extraction
- Portable Executable file parser
- Multiple AV scanner which includes major antivirus vendors:
Vendors status Vendors status Avast ok FSecure ok Avira ok Kaspersky ok Bitdefender ok McAfee ok ClamAV ok Sophos ok Comodo ok Symantec ok ESET ok Windows Defender ok
Installation
Saferwall take advantage of kubernetes for its high availability, scalibility and the huge ecosystem behind it.
Everything runs inside Kubernetes. You can either deploy it in the cloud or have it self hosted.
To make it easy to get a production grade Kubernetes cluster up and running, we use kops. It automatically provisions a kubernetes cluster hosted on AWS, GCE, DigitalOcean or OpenStack and also on bare metal. For the time being, only AWS is officially supported.
Steps to deploy in AWS: (This still needs to be improved)
- Clone the project:
git clone https://github.com/saferwall/saferwall - Using a debian linux, make sure
build-essentialare installed:sudo apt-get install build-essential. - Rename the
example.envto.envand fill the secrets according to which AVs you want to have. - Install it:
make saferwall. - Edit the deployments/values.yaml to match your needs.
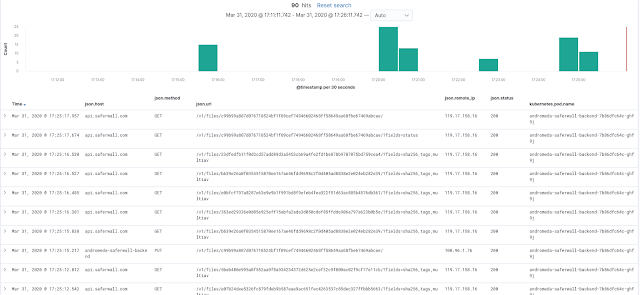
- Logs are found elasticsearch:
Built with:
- Golang mostly.
- Backend: Echo
- Frontend: VueJS + Bulma
- Messaging: NSQ
- Database: Couchbase
- Logging: FileBeat + ElasticSearch + Kibanna
- Minio: Object storage
- Deployment: Helm + Kubernetes
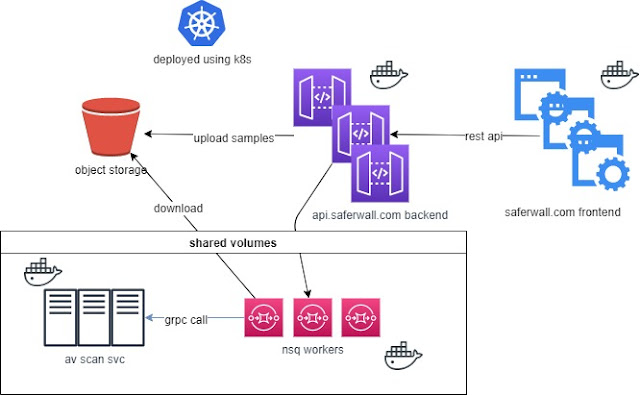
Current architecture / Workflow:
Here is a basic workflow which happens during a file scan:
- Frontend talks to the the backend via REST APIs.
- Backend uploads samples to the object storage.
- Backend pushes a message into the scanning queue.
- Consumer fetches the file and copy it into to the nfs share avoiding to pull the sample on every container.
- Consumer calls asynchronously scanning services (like AV scanners) via gRPC calls and waits for results.
Acknowledgements
- Fangdun Cai for the awesome vue-admin dashboard.
- horsicq for his tool Detect It Easy.
Contributing
Please read docs/CONTRIBUTING.md for details on our code of conduct, and the process for submitting pull requests to us.
[sc name=”ad-in-article”]




















Add Comment