One Security vulnerability assessment/management tool to solve all the security team problems.
What is Jackhammer?
Key Features:
- Provides unified interface to collaborate on findings
- Scanning (code) can be done for all code management repositories
- Scheduling of scans based on intervals # daily, weekly, monthly
- Advanced false positive filtering
- Publish vulnerabilities to bug tracking systems
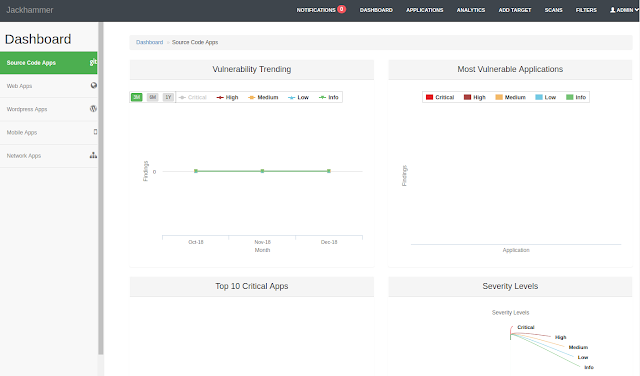
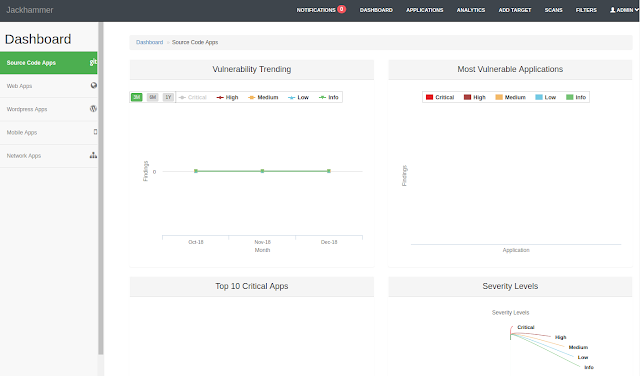
- Keep a tab on statistics and vulnerability trends in your applications
- Integrates with majority of open source and commercial scanning tools
- Users and Roles management giving greater control
- Configurable severity levels on list of findings across the applications
- Built-in vulnerability status progression
- Easy to use filters to review targeted sets from tons of vulnerabilities
- Asynchronous scanning (via sidekiq) that scale
- Seamless Vulnerability Management
- Track statistics and graph security trends in your applications
- Easily integrates with a variety of open source, commercial and custom scanning tools
Supported Vulnerability Scanners:
Static Analysis:
- Brakeman
- Bundler-Audit
- Checkmarx**
- Dawnscanner
- FindSecurityBugs
- Xanitizer*
- NodeSecurityProject
- PMD
- Retire.js
* license required ** commercial license required
Finding hard coded secrets/tokens/creds:
- Trufflehog (Slightly modified/extended for better result and integration as of May 2017)
Webapp:
Mobile App:
- Androbugs (Slightly modified/extended for better result and integration as of May 2017)
- Androguard (Slightly modified/extended for better result and integration as of May 2017)
WordPress:
- WPScan (Slightly modified/extended for better result and integration as of May 2017)
Network:
Adding Custom (other open source/commercial /personal) Scanners:
You can add any scanner to jackhammer within 10-30 minutes. Check the links/video
Quick Start and Installation
See our Quick Start/Installation Guide if you want to try out Jackhammer as quickly as possible using Docker Compose.
Run the following commands for local setup (corporate mode):
git clone https://github.com/olacabs/jackhammer
sh ./docker-build.sh
Default credentials for local setup:
username: [email protected]
password: j4ckh4mm3r
(For single user mode)
sh ./docker-build.sh SingleUser
do signup for access
Restarting Jackhammer
docker-compose stop
docker-compose rm
docker-compose up -dUser Guide
The User Guide will give you an overview of how to use Jackhammer once you have things up and running.
Demo
Demo Environment Link:
https://jch.olacabs.com/
Default credentials:
username: [email protected]
password: [email protected]
Credits
Sentinels Team @Ola
Shout-out to:
-Madhu
-Habi
-Krishna
-Shreyas
-Krutarth
-Naveen
-Mohan


















Add Comment