[sc name=”ad_1″]
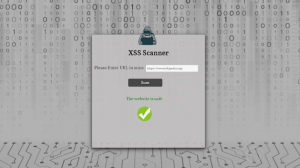
What is cross-site scripting (XSS)?
Cross-site scripting (also known as XSS) is a web security vulnerability that allows an attacker to compromise the interactions that users have with a vulnerable application. It allows an attacker to circumvent the same origin policy, which is designed to segregate different websites from each other. Cross-site scripting vulnerabilities normally allow an attacker to masquerade as a victim user, to carry out any actions that the user is able to perform, and to access any of the user’s data. If the victim user has privileged access within the application, then the attacker might be able to gain full control over all of the application’s functionality and data.
How does XSS work?
Cross-site scripting works by manipulating a vulnerable web site so that it returns malicious JavaScript to users. When the malicious code executes inside a victim’s browser, the attacker can fully compromise their interaction with the application.
What are the types of XSS attacks?
There are three main types of XSS attacks. These are:
- Reflected XSS, where the malicious script comes from the current HTTP request.
- Stored XSS, where the malicious script comes from the website’s database.
- DOM-based XSS, where the vulnerability exists in client-side code rather than server-side code.
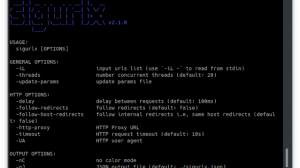
XSpear is XSS Scanner on ruby gems

Key features
- Pattern matching based XSS scanning
- Detect
alertconfirmpromptevent on headless browser (with Selenium) - Testing request/response for XSS protection bypass and reflected(or all) params
- Reflected Params
- All params(for blind xss, anytings)
- Filtered test
event handlerHTML tagSpecial CharUseful code - Testing custom payload for only you!
- Testing Blind XSS (with XSS Hunter , ezXSS, HBXSS, Etc all url base blind test…)
- Dynamic/Static Analysis
- Find SQL Error pattern
- Analysis Security headers(
CSPHSTSX-frame-options,XSS-protectionetc.. ) - Analysis Other headers..(Server version, Content-Type, etc…)
- XSS Testing to URI Path
- Testing Only Parameter Analysis (aka no-XSS mode)
- Scanning from Raw file(Burp suite, ZAP Request)
- XSpear running on ruby code(with Gem library)
- Show
table base cli-reportandfiltered rule,testing raw query(url) - Testing at selected parameters
- Support output format
clijsonhtml- cli
- json
- html
- Support Verbose level (0~3)
- 0: quite mode(only result)
- 1: show scanning status(default)
- 2: show scanning logs
- 3: show detail log(req/res)
- Support custom callback code to any test various attack vectors
- Support Config file
Installation
Install it yourself as:
$ gem install XSpear
Or install it yourself as (local file / download latest ):
$ gem install XSpear-{version}.gem
Add this line to your application’s Gemfile:
gem 'XSpear'
And then execute:
$ bundle
Video:
https://youtu.be/RM1NM4EDRo8
[sc name=”ad-in-article”]



















Add Comment